NSA’s ECHELON: The Predecessor of PRISM
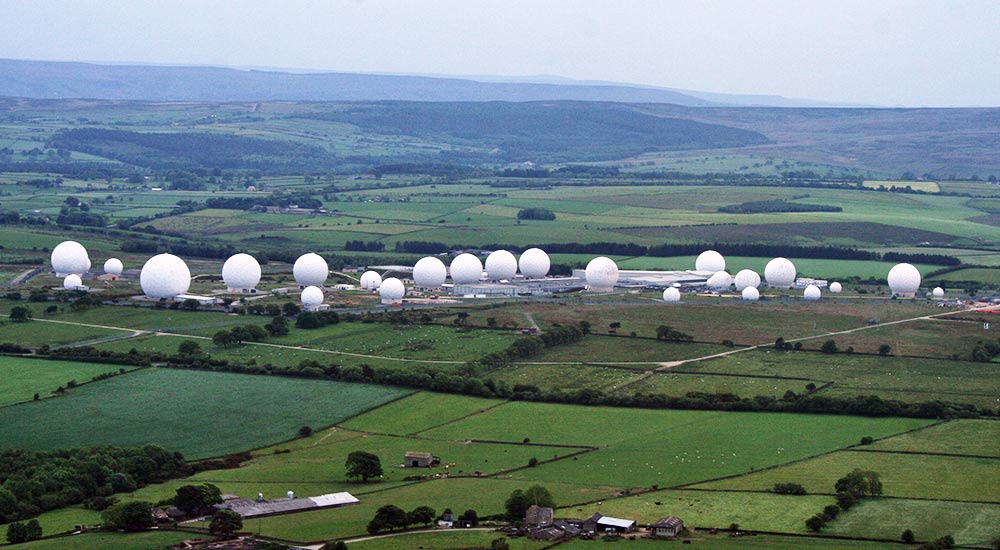
RAF Menwith Hill – Photo by Mark Morton | CC-BY-SA 2.0
2013 has been a really tough year for the National Security Agency (USA), giving a fieldwork for the other agencies that are in cahoots with them on this massive global eavesdropping saga. One of their contractors, Edward Snowden, has exposed some key top secret and classified documents on several mass surveillance programs under the codenames PRISM, XKeyscore, Tempora, Muscular, Project6, Storeroom, and Lustre.
While the developing reports of the PRISM documents are alarming, the history of PRISM itself is even more disturbing, as it roots back to the Cold War times to a surveillance program by the name ECHELON, developed at an RAF base in England, Menwith Hill.
ECHELON, NSA, and the UKUSA
ECHELON is the first global surveillance program that was introduced by the NSA, right when global communication was at its nascent stage, rooting back to 1947. Though the program was primarily formed to spy on the Soviet Union and its allies during the Cold War, it evolved to extend towards domestic and industrial espionage as the computing power grew.
A Lockheed employee, Margaret Newsham, one of the first sources who confirmed the existence of ECHELON, had claimed in interviews to a Danish publication that ECHELON was one of the costliest, sophisticated, and biggest intelligence programs by the NSA.[1] And according to her, the name ‘ECHELON’ was initially the name of the computer network developed by Lockheed for the NSA and was used both in the United States of America and the United Kingdom.
And various other disclosures also indicates that the primary dwellers at the Menwith Hill were mostly US employees[2] of the NSA, confirming the covert marriage of both the countries by the UKUSA agreement––which would later form the Five Eyes, comprised of the United Kingdom, United States, Canada, Australia, and New Zealand. More reports and disclosures can be found here.
ECHELON and Microsoft
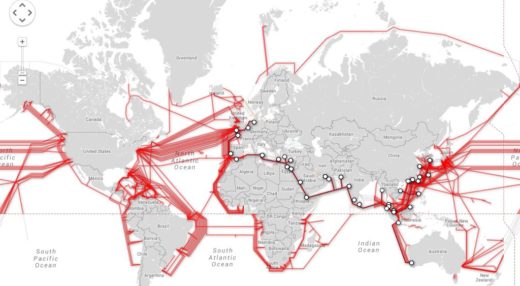
ECHELON had its grip on all global communication channels since its infancy, from telephone lines to the early domestic computers, all tapped via tailored hardware, cable taps, and even satellites to search for keywords that are compiled from records called the echelon dictionaries. And it isn’t a surprise to know that Microsoft, one of the popular operating system vendors in the mid-90s, was in on the ECHELON program as well.
_NSAKEY
On the Windows operating system, CryptoAPI (CAPI) is how developers can access the cryptographic services to use encryption in their windows applications. Microsoft provides a key that can be used to digitally sign any applications that needed encryption so Microsoft can validate it. But when they released the service pack 5 to Windows NT 4, a security researcher, Andrew Fernandes, identified a second key that existed with a name ‘_NSAKEY’.[3]
When the report was published at a conference, Microsoft, eventually claimed that the name of the key was just to state that it qualified the NSA standards, and it was nothing but a spare key.[4] As a matter of fact, the US government had restrictions on shipping encryption capabilities outside their country. And by law, Microsoft had to comply by having their key as per the standards set by their regulatory authority.
But given the power of ECHELON, Microsoft’s cooperation with the NSA, FBI, CIA in circumventing their own encryption to let free access for the government to Outlook services, Skydrive, and Skype in PRISM, the Windows 8 Trusted Computing debacle, it is now hard to believe that the _NSAKEY was just a spare key as Microsoft claims it to be.
NSA’s industrial espionage
ECHELON’s capabilities have been exploited multiple times by the NSA for the competitive gains for the American market and private American companies. This includes aiding the CIA with eavesdropping resources to whistleblow on Thomson-Alcatel––so Raytheon, an American company could secure a Brazillian government deal. NSA also blew the whistle on Airbus when they tried to bribe the officials of the Saudi Arabian national airline––so that Mcdonnell Douglas, another American company could secure that deal. A similar incident was disclosed when the CIA eavesdropped on conversations between the executives of Nissan and Toyota and the Japanese government officials––so that America could have an upper hand in trade negotiations with the Japanese at that time. And down the line ECHELON network was also used to steal a patent from a German wind turbine company Enercon.
With the recent leaks, it is clear that ECHELON 2.0 aka PRISM has been able to infiltrate several other sectors with a clear intention of industrial espionage, inflicting damages in billions.
Why ECHELON and PRISM sound scary?
The usual statements defending the global surveillance bring forward the significance of the scrutiny of global communication channels that would align with national security interests of the Five Eyes mutually.
But evidence and disclosures suggest that this was not the case with ECHELON or PRISM (ECHELON 2.0). Normal people are spied on every day. Private communication channels between average citizens are breached. And the entire program was used with different intentions than for national security.
There is a clear possibility that both these programs have violated, breached, and exploited the very basic right to privacy of a human being. What makes this disgusting is that these programs are sanctioned by the very government that is supposed to be protecting the citizens from such inhumane things. A full detailed report on ECHELON was presented at the European Parliament, listing out the concerns and damages by the program.
The Surveillance Headquarters
Menwith Hill in Britain, the birthplace of ECHELON and the largest signal intelligence gathering site in the world established by the United States and the United Kingdom, is now undergoing a major expansion under the codename ‘Project Phoenix’––since 2012 and expected to be completed by 2015. It is speculated that this expansion could probably be the Five Eyes trying to upgrade their infrastructure.
PRISM, quantum computing, and NSA
A common speculation/conspiracy theory around these SIGINT sites is that one of them, like this particular RAF base, could be housing a quantum computer development or a supercomputer that could be slaved towards breaking modern encryption.
But this is highly unlikely and mathematically impossible even with quantum computers. But what is possible is that they might already have the resources on breaking the ‘breakable’ encryption or mere metadata computation to plant backdoors and remote access tools, which is what PRISM is mostly all about.
Safeguard yourself
Thanks to the documents leaked by Edward Snowden, the involvement of major tech conglomerates like Google, Apple, Microsoft, Facebook, in this mass surveillance program is now blatantly exposed. As a common citizen, you can safeguard yourself for now with open-source, end-to-end encrypted platforms and applications. We have written a definitive guide on choosing the best private and secure messaging application. We have also written about PRISM and TAO (the unit within the NSA armed with an arsenal of hacking resources) here.
I have merely covered about ECHELON and PRISM. There are a plethora of reports on various other clandestine surveillance programs from different agencies around the world available on the internet. Do your research and stay safe by using the right medium to communicate. Explore our surveillance section for more resources.
Footnotes
- “Interview: ECHELON Was My Baby.” Cryptome.org. N.p., 2015. Web. 24 Jul. 2015.
- Norton-Taylor, Richard. “Menwith Hill Eavesdropping Base Undergoes Massive Expansion.” the Guardian. N.p., 2015. Web. 24 Jul. 2015.
- “CNN – NSA Key To Windows: An Open Question – September 3, 1999.” Edition.cnn.com. N.p., 2015. Web. 24 Jul. 2019.
- “Microsoft Stonewalls NSA_Key Questions.” Cryptome.org. N.p., 2015. Web. 24 Jul. 2015.
This post was first published on January 5, 2014.