NSA’s Offline Surveillance: Radio Penetration via Hardware Implants
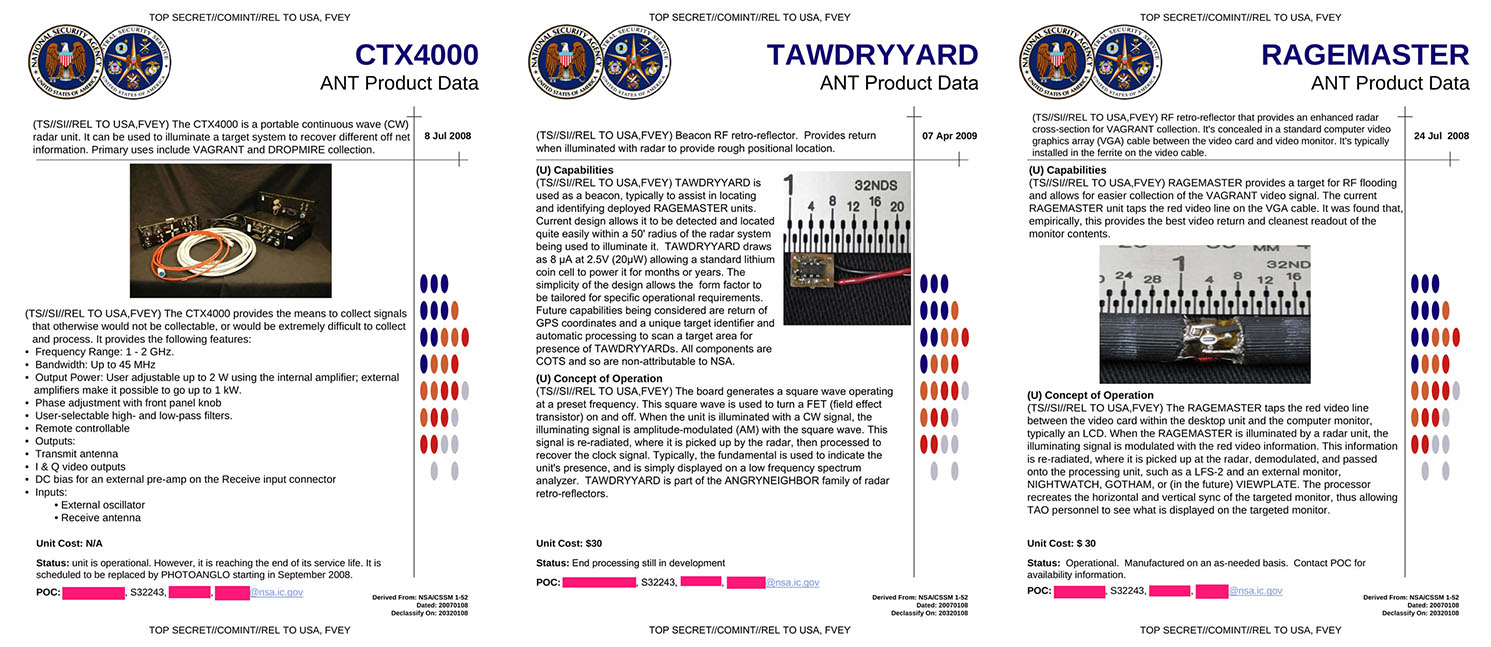
A few days ago, Der Spiegel disclosed a few hardware components from the NSA’s ANT catalog and there was a serious debate if NSA could have the potential to get into the devices even when they are not connected to the internet or powered off. As I’ve mentioned in this article, the NSA’s CTX4000 is a portable continuous wave radar unit that is used to spy on the systems that already had the other secret hardware implants, placed either by an agent or by the manufacturer. In some extreme cases, it is believed that the NSA used to track the components and plant the hardware during the time of transit.
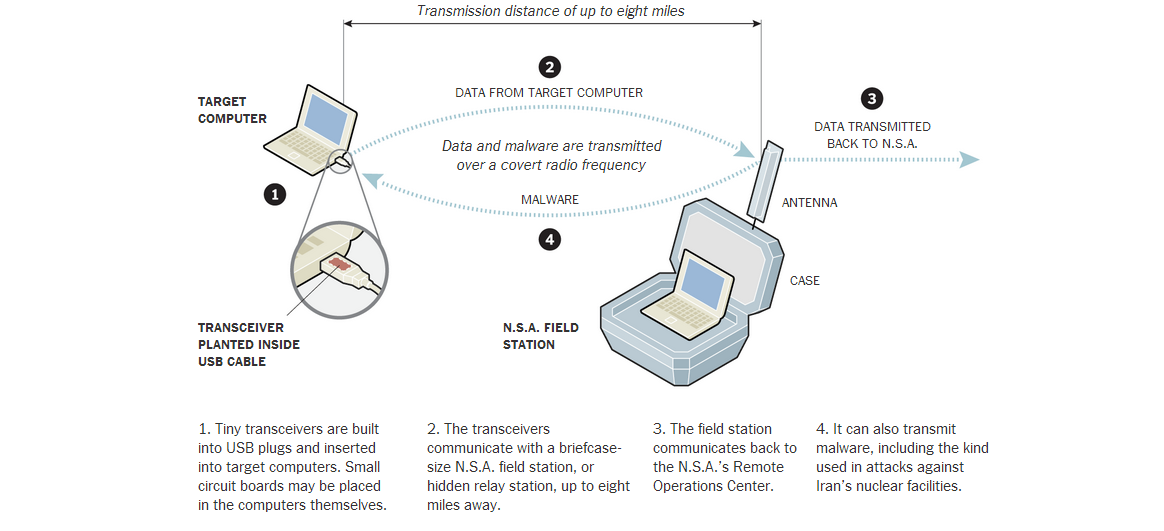
From this piece of article from The New York Times, it is clear that the NSA did house such technology capable of penetrating and spying a target’s computer or any other device with the aid of such devices. The most common devices are found to be planted in the USB devices and circuit boards covertly. These devices use a covert radio frequency channel to transmit data to a nearby portable base station around 8 mile radius.
Besides this penetration, the QUANTUM program also widened the NSA’s windows to successfully exploit devices with help of 100,000 implants. The Computer Network Exploitation had targeted Russian military networks, European trade Institutions and some countries like Saudi Arabia, India and Pakistan as per The New York Times report.
The NSA’s ANT catalog is expected to house more powerful tools than the disclosed one. Further disclosures could show us the clear sky and elucidate the fuzzy stories around the little hype surrounding this scandal.
Image[2] Courtesy: The New York Times
This post was first published on January 15, 2014.








2 Responses
[…] Swipes: NSA’s Offline Surveillance: Radio Penetration via Hardware Implants An Overview on NSA’s TAO – A Shocking Revelation Boeing Black Smartphone Self-Destructs When […]
[…] Swipes: NSA’s Offline Surveillance: Radio Penetration via Hardware Implants An Overview on NSA’s TAO – A Shocking […]