Will You Trust an Untrusted USB Device?

There are some potential threats involved in browsing an anonymous USB flash drive. The severity of the attack depends on how paranoid the user is and how limited is the attacker’s imagination. Chances are some malware will be activated on opening the folder or just by plugging it in the computer. The hacker may use the exploits or any back door vulnerabilities in the OS and probably operate through any of the detected bugs and bring the malware into action.
Operation Buckshot Yankee is a US cyber defense strategy operated by Pentagon when the military networks were under potential threat in 2008. Apparently, someone left a flash drive in the car parking area of a DoD base in the Middle East and it was picked up and later inserted into a US military laptop. The malicious computer code inside it was uploaded by itself and spread onto classified and unclassified systems, establishing a digital foothold from which the data can be transferred by servers under the influence of the hacker, who is outside the domain.
Come on, a rogue program that can control the systems remotely? Definitely, James Bond stuff.
The military networks were also infected by a worm named agent.btz, which is a variant of a sillyFDC worm that has the ability to scan computers for data, open backdoor, and send through those backdoor to a remote command and control server.
However, the nightmare would be if the flash drive, whose source is unknown, is something like the USB rubber ducky, a programmable key-logger as well as a keystroke injection tool. It deceives the users with its appearance as a normal flash drive and when plugged, it records or injects the keystrokes of the user into the system.
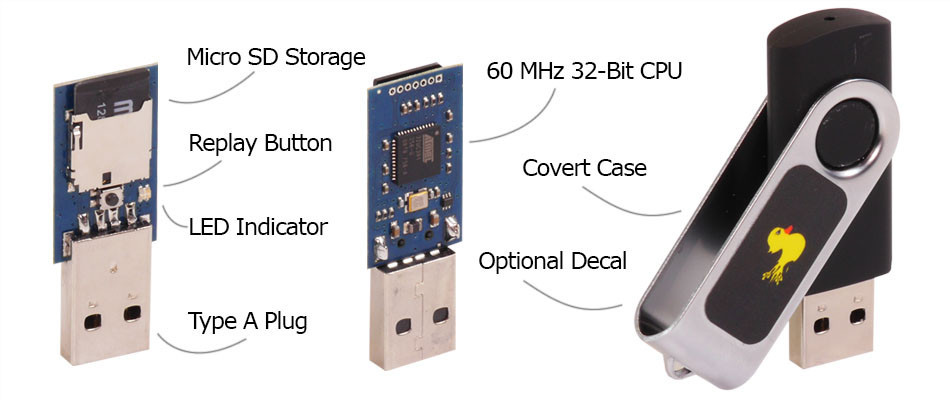
It registers itself as a keyboard and it can enter whatever sequences of keys as it pleases. The product would contain a website, which includes scripts for multiple operating systems that can be stealthily deployed against a target computer. The created scripts would fall under three categories: Reconnaissance, Exploitation and Reporting. Scripts from all three categories could be mixed together, allowing the user to create a payload suited for their situation. Reports would be generated containing information collected about the target computer based on the user’s selection and then delivered to the user via one of the Reporting methods. The information within these reports could range from installed software to network information.
The other concerns would rise for the common malware, which are likely to be jolted by the thumbnail renderer of your windows explorer. PDF based, exploits are the common backdoor for some Trojans and malware, that are passively activated by the windows itself even when the drive is not opened.
Although one can argue, it is better not to insert and browse a completely unknown drive; the most that can happen is loss of files or intrusion. Though some precautionary steps like, disabling the autorun feature or scanning the drive before opening or using the drive, it is always good to ignore that mysterious flash drive, unless it is considered vital for the survival of the human race.
Image by Anton Fomkin | CC BY
Related Swipes:
NSA’s Offline Surveillance: Radio Penetration via Hardware Implants
An Overview on NSA’s TAO – A Shocking Revelation
This post was first published on March 3, 2014.