On Privacy and Security of Smartphone Biometrics
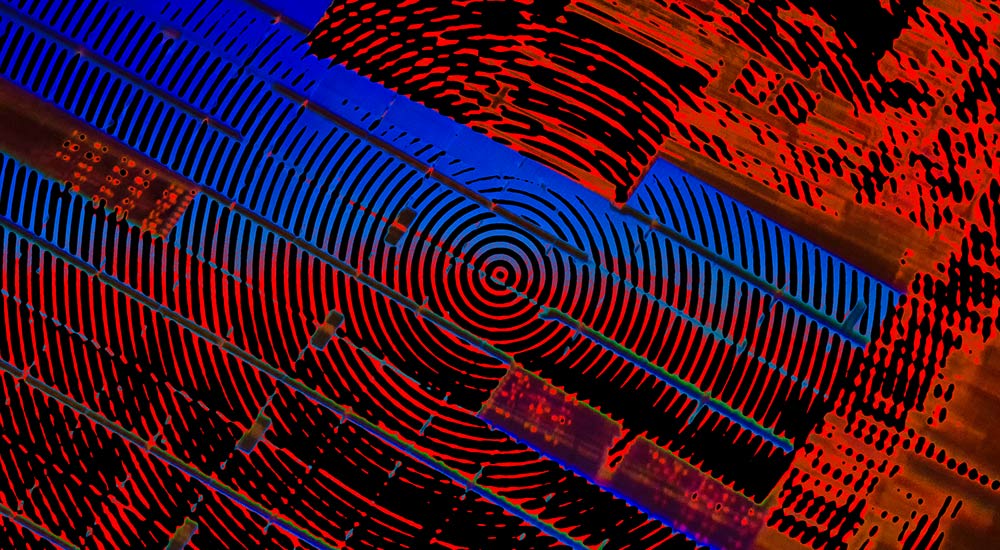
Every smartphone in the wild these days come equipped with face detection capability coupled with a fingerprint sensor. But how far do you think you can secure your device with biometrics? Would you trust a company with your fingerprints and facial scan data?
Biometrics and privacy
On computers, there are many critical stuff that requires secure and isolated storage where no one—not even the user or manufacturer—has access to. Cryptographic processes—the encryption and decryption—are one such critical component that needs physical isolation from the main processor and memory.
For such processes, a computer usually has a dedicated processor on the motherboard called as the Trusted Platform Module. The TPM is isolated from the main processor with its own memory, OS, and an API. This is where all critical cryptographic processes take place—with a practically impenetrable hardware security layer for the keys.
In a similar fashion, smartphones have a specific environment in the processor for handling sensitive data executions like content protection (DRM) and biometric data processing. This isolated space is called the Trusted Execution Environment.
The TEE provides an isolated environment that encrypts your fingerprint and other biometrics that your device supports, hardware-level isolation for the encrypted data, tamper protection, and safety measures against reverse engineering.
So when you set up your fingerprint or capture your facial data for the first time, the data gets encrypted and stored in the TEE. And the rest of the applications are only limited to a true or false response from the TEE API and not the actual decrypted biometric template.
Biometrics and security
Passwords can be changed as many times as you want. You can’t do that to your fingerprints, can you? Duh! So yes, you are technically walking around slapping your password everywhere for the world to take.
With a motivated criminal mastermind on the loose, you could have your device stolen, fingerprints lifted off that glass window where you window-shopped, and had a latex glove made with your prints on it that would have already unlocked your phone several times.
Fingerprints are just your identity. The stuff you use to authenticate yourself to your smartphone. An extra layer of a password is what gives that security element for your device. Now that you know this better. Stay secure with passwords. And don’t forget to take care of the webcams and microphones.
This post was first published on September 28, 2013.








1 Response
[…] system or if allowed by privacy laws, user biometrics. And this is how you exactly need to use biometrics—to authenticate your identity and not as a damn […]