You think you are in luck finding a USB device in the parking lot? You know well that it is a shady trap to loot all your data! So for the curious minded who would love to safely open the USB and explore its contents, here are some ways to do it.
Make sure it’s not a USB killer
USB killer is a device that looks like a typical USB flash drive but designed specifically to destroy any device that you plug into. USB killers have huge capacitors inside the casing, which is capable discharging at 240 V — enough to permanently damage your computer or phone. While most of the latest models of notebooks and mobile devices are protected for high voltages, you really don’t want to risk anything for some random USB you got from an untrusted source.

So open it up and make sure that the device you have is actually a flash drive and doesn’t have any custom built electronics or unusually large capacitors inside it. For reference, a USB killer might look like the one in the above pic. Note how big the capacitors are. To avoid accidentally plugin in an unknown USB killer, it is recommended that you use USB hub that protects against such discharges.
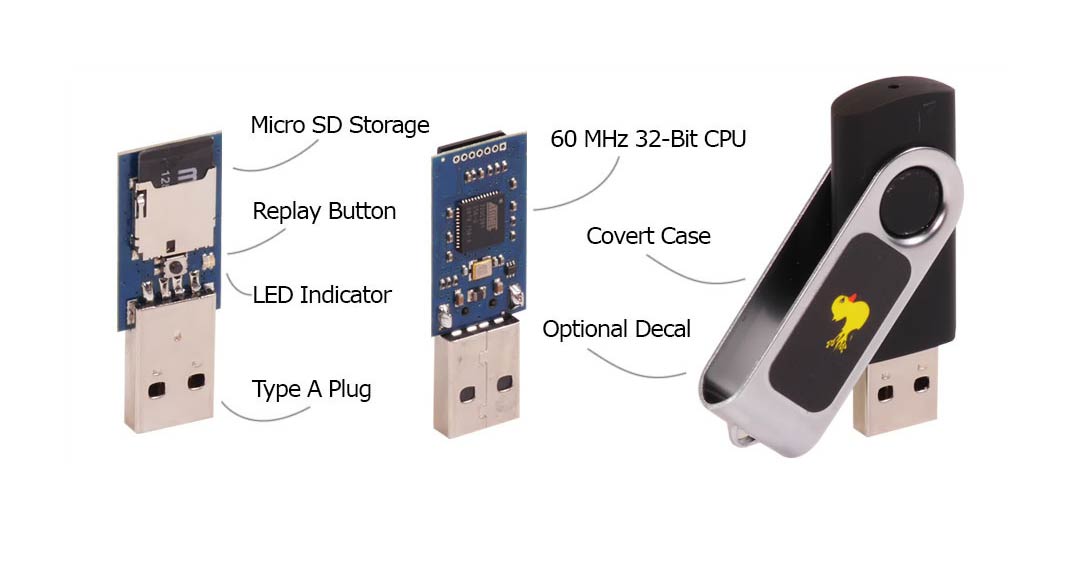
Make sure it’s not a USB Rubber Ducky
Rubber Ducky is another USB device that originally is a keyboard that is controlled by a microcontroller on the main board. Once connected to a computer, the Rubber Ducky as programmed, injects the intended malicious payloads from its internal MicroSD card. Here are some of the scary payloads to give you an idea what sort of things can be done with such device.
Spotting a USB Rubber Ducky could be tricky at first glance. When you open up the case of the device, a Rubber Ducky board should look like something in the following picture.
Use a live CD with a Linux distro to access the untrusted USB
Most popular Linux distributions can be booted directly from USB devices. Download one, boot into it from your USB, and now safely read the contents of the other untrusted USB drive you just found. As a USB booted Live OS would use only your RAM, nothing malicious would ever get into your hard disk. But to be on a safer side, disconnect all your hard drives before you try this.
Use an OS, running inside a virtual environment
Though you can turn off autorun in your Windows OS, or mount the USB as readable on a Mac, you shouldn’t be betting your luck by plugging the device in your primary OS. If it is something like a Rubber Duck or even a device with loads of malware, it will be a disaster. So to ensure the safety of your computer and whatever data is in it, a sandboxed virtual environment is the recommended way to explore the contents of the untrusted USB.
Technically, a virtual machine is the least safer way available to access a random suspicious USB device. Like any software, virtual machines are vulnerable too. For devices that are too suspicious, we recommend using the VM on a spare computer, or the better — a live OS from your USB, with networking and hard drives disconnected.
You shouldn’t be peeking into other people’s USB devices, but you may need to if you intend to find the owner of the device to return. In that case, we hope this edition is helpful.


Is disabling autoplay enough? Where do I find the autorun settings?
Perhaps a quick way to test a bad USB is plugging it into a Raspberry Pi unit.
Or a friend’s computer!
with friends like you…
Use the computer in the business office , for residents in the complex you live at
Did not know that USB drives can fry out a system. This is some wicked stuff!