GOTCHA – a Better and Beautiful Alternative to CAPTCHAs
For the life of me, I can never stand typing those severely distorted words or keep training Google’s classifiers on reCAPTCHA—with each click lasting for a decade with a fade in time of 5 seconds. With very high hopes, I see GOTCHAS as an abstract and enjoyable alternative to CAPTCHAs.
Generating panOptic Turing Tests to Tell Computers and Humans Apart
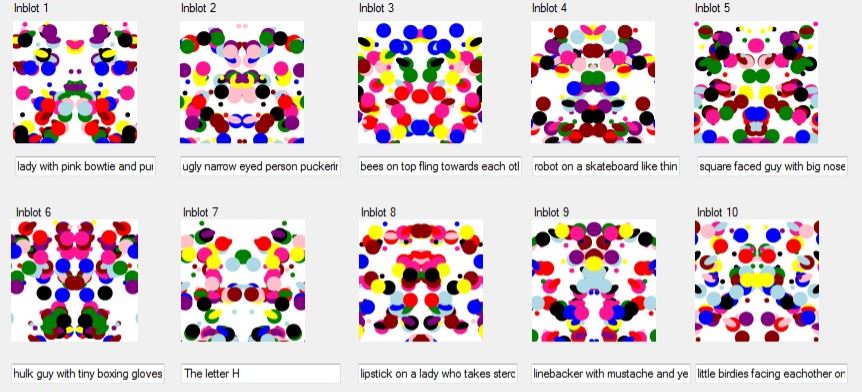
Yup! That’s what GOTCHA stands for. GOTCHA works by generating coloured inkblots based on the user-submitted password when he first signs up for a site. Once the inkblots are generated, the user would then have to describe each of the images in their own phrase. This data is then saved on the server for future Turing tests.
Generating panOptic Turing Tests to Tell Computers and Humans Apart
Now if the user visits the site again and tries to login with his password, the inkblots and phrases (randomized) are shown as a puzzle. Only when the user could match the phrases with the corresponding inkblot he would be authenticated. As this can only be solved by a human (for now) in real-time, any sort of bot attacks can be virtually eliminated.
Challenges
While the research relies on the premise that human beings recognize patterns easier and quicker, it is inevitable that eventually, chaos would ensue if users forget how they described their patterns in the first place. It’s been four years and I still can’t remember the correct key combinations for my front door!
GOTCHA sure is an evolution over CAPTCHAs that are susceptible to automated computer attacks, but the practical application of GOTCHAs need to start somewhere and it’s doesn’t exist anywhere. Also, the system needs a rigorous test and address usability features like optional inkblots for scenarios where inkblots are too ambiguous to describe.
A better alternative to CAPTCHAs
CAPTCHA implementations partly depend on the size of your application. For a larger site where the user interest is too high, it’s probably good to stick with well-tested CAPTCHA services like reCAPTCHA (if you’re a dev reading this, for the sake of everyone’s sanity, please set it to low or moderate so we don’t have to sit around for a day solving images) as they are immune to automated attacks to a certain level.
For small projects and internal applications, you could use a simple arithmetic or word based CAPTCHA implementation, while keeping an eye on incoming threat vectors and bot types. There are also solutions like Honeypot (where you add some extra hidden fields and wait for the bots to fill it so you can distinguish human inputs apart) that perform better and time-based CAPTCHAs (it’s a hit or miss if a user solves CAPTCHAs at the speed of a bot) if you are inclined against third-party CAPTCHAs.
A less annoying solution compared to all the above methods is to use the two-factor authorization system or if allowed by privacy laws, user biometrics. And this is how you exactly need to use biometrics—to authenticate your identity and not as a damn password!
This post was first published on February 8, 2014.








Intuitive research but seems like too much work for something that can be solved with 2FA.
A bat! Wing! Blobs! Colorful blobs! Clown! Get ready for the ‘list of most commonly used GOTCHAS’!
Every people thinks differently when seeing an abstract picture. How is this different from other CAPTCHAs?
When using a conventional CAPTCHA the images shown to you also need to be shown to many other users to gather an acceptable data to verify it with. But GOTCHA is generated uniquely for everyone.