Delete Windows System Folder
When you are dealing with a secondary drive or trying to use an old system drive as a storage device, you might want to get rid of the files and directories created by Windows. But Windows’s system files are owned by SYSTEM or TrustedInstaller by default and they do not provide full directory access control to any of the normal users, including the administrators.
To do that, you’d usually navigate to the files in the explorer window and use the properties window of the system directories to take control of the directories so that you can remove them the usual way. But if you are reading this, you might have hit a snag or find the whole process a hassle. In those cases, use the following three commands from an elevated command prompt to finish the job quicker.
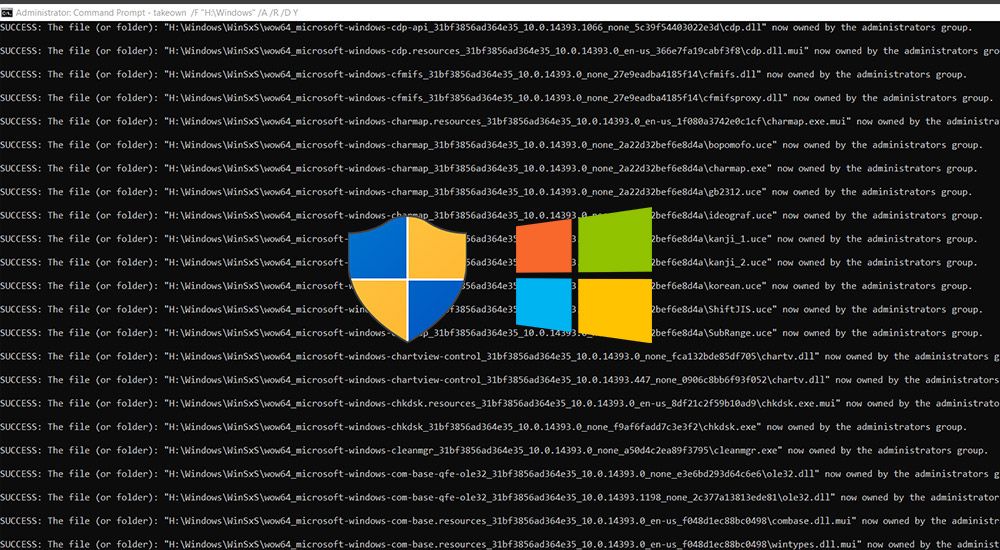
takeown /F "H:\Windows" /A /R /D Y
icacls "H:\Windows" /T /grant administrators:F
rd /s /q "H:\Windows"Replace the H: with the drive letter of the drive you are trying to delete system folders from. The first two commands recursively change the ownership of the system directories (like the Program Files and Windows folders) and subdirectories to the administrator user, and grants the full access control. The third command finally removes the directory.
This post was first published on March 5, 2014.