An Overview on NSA’s TAO – A Shocking Revelation
There is been a vast hype about the NSA’s mass surveillance since the whistleblowers released a few critical documents, that mostly exposed the entire scheme of the mass surveillance, by the NSA with the help of its allies. As the speculations began to stir up people all over the world, I decided to clarify myself if I’m going to stay ‘okay’ with all the surveillance stunts. And at the right time, my friend asked me if the surveillance is going to affect an ordinary non-US person who uses the internet for a very little social time and entertainment. Initially, I hoped that the ongoing debate on the surveillance is actually the best way to find if the national security desperately needed to take such an immense measure to protect its people. Soon when I learned about the complete structure of the surveillance program, my mind rendered the debate obsolete, and I realized how hard a normal person is wedged by the surveillance techniques.
TAO
TAO, the heart of NSA’s hacking unit, is the first that faded in to the spotlight, when I looked. Tailored Access Operations is the unit that leverages the computer vulnerabilities and uses them against the target by infiltrating the machine with malwares that spy on the machine or the machines connected to the network. As the NSA agents call it as ‘Computer Network Exploitation’, the unit actually receives their metadata for potential exploiting chances via XKeyscore, another NSA tool that stores the entire data of a target in records, for an ease of access for other internal analysis. It is more like a search engine for the metadata. The exploits are way too easier for the unit as the vulnerabilities of Microsoft, Huawei, Cisco and a list of manufacturers are usually easy to be detected with the help of the crash reports submitted by the user (in case of windows) and more sophisticated methods for the other machines like the man-in-the-middle-attack approach. The TAO has already succeeded in hindering Iran’s nuclear program with such an attack.
Stuxnet
Stuxnet is a popular TAO malware believed to be created by the NSA with the aid of Israeli intelligence to sabotage the nuclear facilities of Iran. The malware affected the industrial control system and resulted in malfunctioning of over 1000 centrifuges that are controlled by the SCADA systems. The malware was infiltrated in variants, and despite its primary objective, Russian and Iranian power plants were also added to the victim list in a few months from the initial attack.
When the end point is enlarged visually, one could find that the end victim of these attacks and interception will be that one person who spends some happy time on the internet, and even his old neighbor who have no idea what an internet is. Well, the quest still continued to find a strong impact that bridges a direct contact with the big brother stunt.
It Just Got Bigger
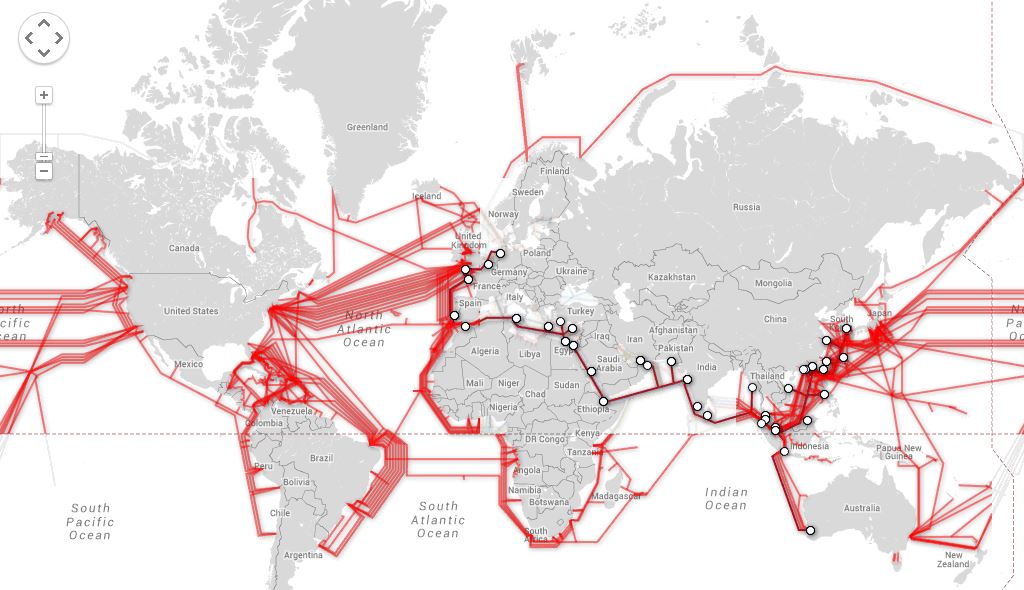
As more documents started to surface, the eavesdropping scandal inflated when those presentations revealed that the submarine communication cables laid across the ocean was also tapped by the NSA and GCHQ. The two cables SEA-ME-WE 3 and SEA-ME-WE 4 are believed to be spied by the two national signal intelligence agencies probably with the aid of USS Jimmy Carter. They’ve also used a technique called QUANTUMINSERT to hack some high value targets in OPEC and Belgacom using the access from its covert infrastructure of hidden servers. It is evident that the spying of the underwater cables is a huge advantage for the five eyes, to collect traffic data globally and analyze them at their convenience with the help of their sophisticated armory of tools listed in the NSA ANT Catalog.
NSA ANT Catalog
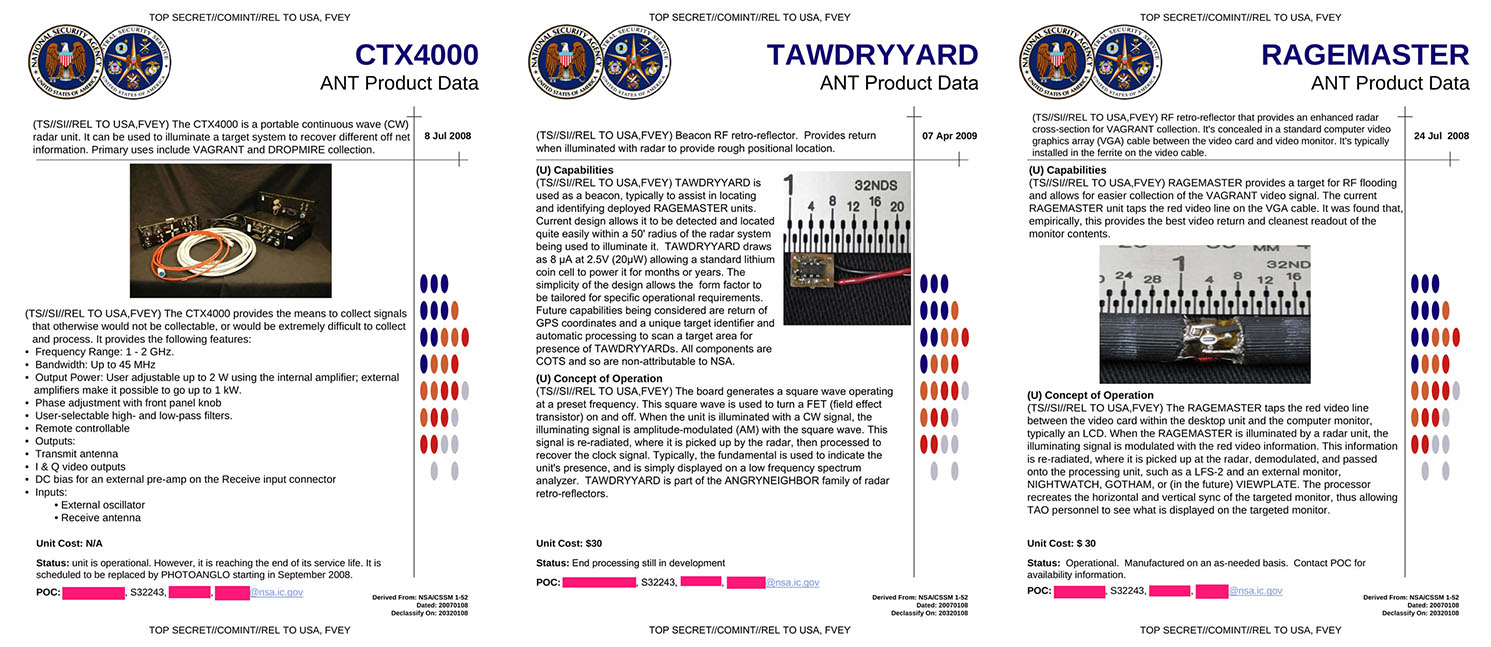
Yep! It is a catalog for the TAO unit comprised of all the tools and technologies available for their mass infiltration and spying operations. Now the exploration of the list might indeed sound a bit scary as they finally happen to have the potential to affect a person physically. As mentioned in Der Spiegel, a German magazine, the catalog houses tools and devices that actually are capable of emitting high power RF signals which might be undesirable and harmful for human body (which is not!). The equipment CTX4000—now replaced by PHOTOANGLO—is one such device which reveals the signals emitted by a computer or any device. This cuts off the installation of a hardware implant or bug in the victim’s computer which can be detected by emitting waves. Rather, the combination of a few devices like RAGEMASTER (Video interception tool), LOUDAUTO (A retro-reflector device), TAWDRYYARD (A beacon to find the implants) are used as implants as they emit faint signals and are undetectable. The bugging usually takes place during the transit of the item when the person of interest purchases a new hardware. The fifty page catalog can be appended with undisclosed tools and some commonly known tools like a normal GPS tracker, Automatic license plate detection systems and more tools that could find its way into the digital device from common vulnerabilities.
Tip of The Iceberg
If the Americans and Israelis could setback a nation’s nuclear program with a malware, the things the NSA could actually do to any nation with these perfectly tailored off the shelf tools, and thousands of hackers, could be as disastrous as the ‘Die Hard 4.0’ movie. From injecting malwares to intercepting the parcels and bugging the devices, the NSA is potentially dangerous malfunctioning government agency with an evil schema, no matter how legitimate they claim about defending the nation. As far as we know about the NSA, GCHQ and the potential of their mass surveillance program, we are clear that if it weren’t for the whistleblowers, they could’ve even extracted our genetic information and would’ve gone beyond the current status of their surveillance. So far we’ve just seen the tip of the iceberg and still there are more undisclosed documents that could reveal the rest of the NSA’s agenda.
The Common Person
When you circle back to the prominent question if a normal person is affected by the surveillance, you could figure out the square answer by now. Even if the person is off the grid, the metadata from his friends will easily channel to him. There is always a way for the NSA to get to that person with the interconnected nodes of his friends, family, workers and acquaintances of social media. Besides, if that person happens to live around a High Value Target, the beacons and high energy waves will certainly put him in between the cross hairs. And moreover, no one likes to have their emails read, phone conversations, personal files scanned my anonymous people—especially the government people.
Similar Swipe:
NSA’s ECHELON: The Predecessor of PRISM
This post was first published on January 8, 2014.







Please publish all the disclosed documents!
We don’t have access to any disclosed documents or any direct contact with leaked sources. We will try our best to publish the key disclosures once they surface.
ROFL